Introduction about Internet Services#
FortiGuard Internet Service offers a database of Internet applications, complete with corresponding IP addresses, port numbers, and transport protocol. The database is routinely updated to include newly published service attributes such as ASNs, geographic information, IP reputation, and popularity metrics.
Internet Service can be applied as source and destination parameters in firewall policies. However, internet service can also be used as a matching condition for SD-WAN rules and traffic shaping policies.
The Internet Service Database (ISDB) stored on a FortiGate can be configured with different sizes of numbers of addresses: mini | standard | full | on-demand. The default configured value depends on the FortiGate model. FortiGate models with 2GB of memory are recommended to use on-demand database. To manually set the ISDB size use the following:
config system global
set internet-service-database {mini | standard | full | on-demand}
end
Get the list of Internet Services from the online ISDB: https://www.fortiguard.com/updates/isdb
Using Internet Service in a Firewall Policy#
Reference: FortiOS 7.6.4 Administration Guide - Using Internet Service in a policy
You can apply three different types of Internet Services to a firewall policy:
- Predefined Internet Services
- Custom Internet Services (see FortiOS 7.6.4 Administration Guide - Using custom Internet Service in policy)
- Extension Internet Services (see FortiOS 7.6.4 Administration Guide - Using extension Internet Service in policy)
Following, two cases are presented where Predefined Internet Services are used.
Case 1 - Simple Use Case#
A specific user with static IP 10.100.88.100 needs access to GitHub repositories on the internet. All other traffic destined to internet should be blocked for this user. At the moment, an existing firewall policy is in place blocking user access to the internet. DNS queries are permitted and sent to an internal server.
To enable the user access to GitHub repositories on the internet, a firewall policy with GitHub Internet Service is configured following these steps:
- Go to
Policy & Objects > Firewall Policyand clickCreate New. - Click in the
Destinationfield. - In the
Select Entriespane, selectInternet Servicefrom the dropdown list and search for “GitHub”:
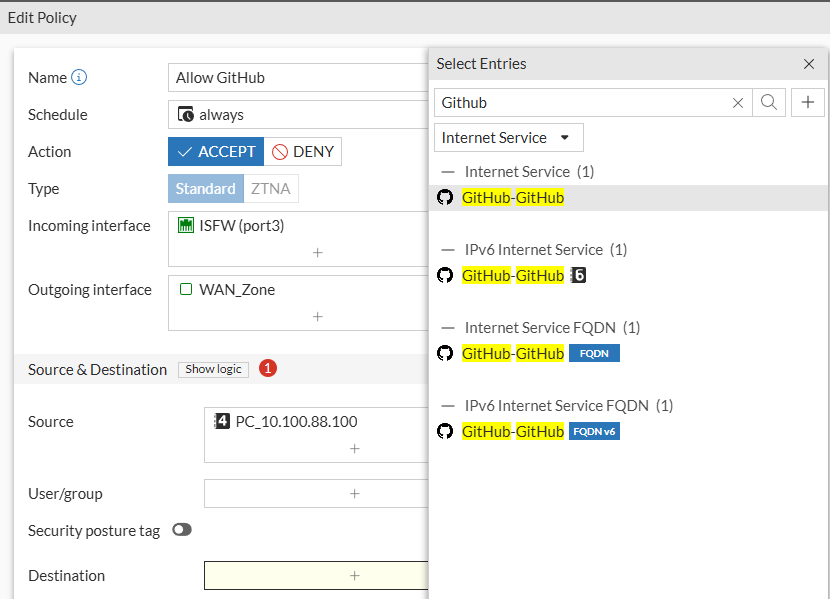
From the list, different options are available, IPv4/IPv6 IP-based and FQDN-based internet services. Hover over each Internet Service to see their respective details:
- IPv4 Internet Service:
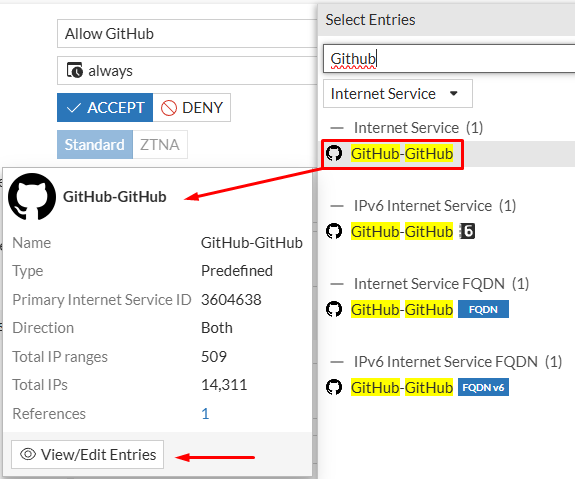
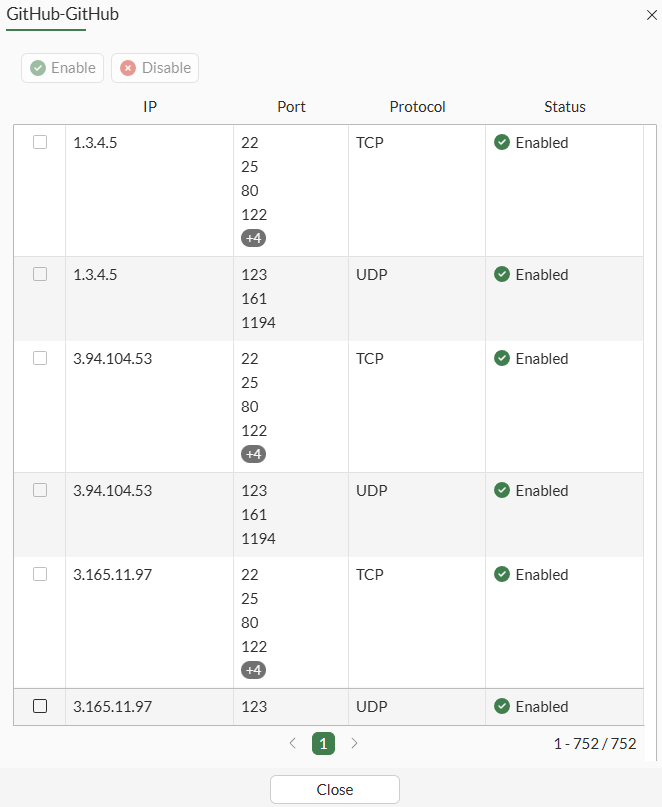
Clicking on View/Edit Entries:
- IPv4 Internet Service FQDN:
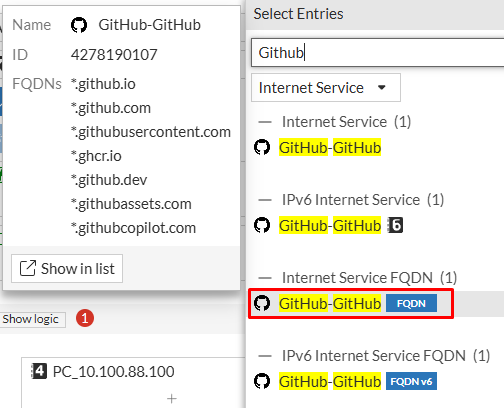
- Select the IPv4 Internet Service option:
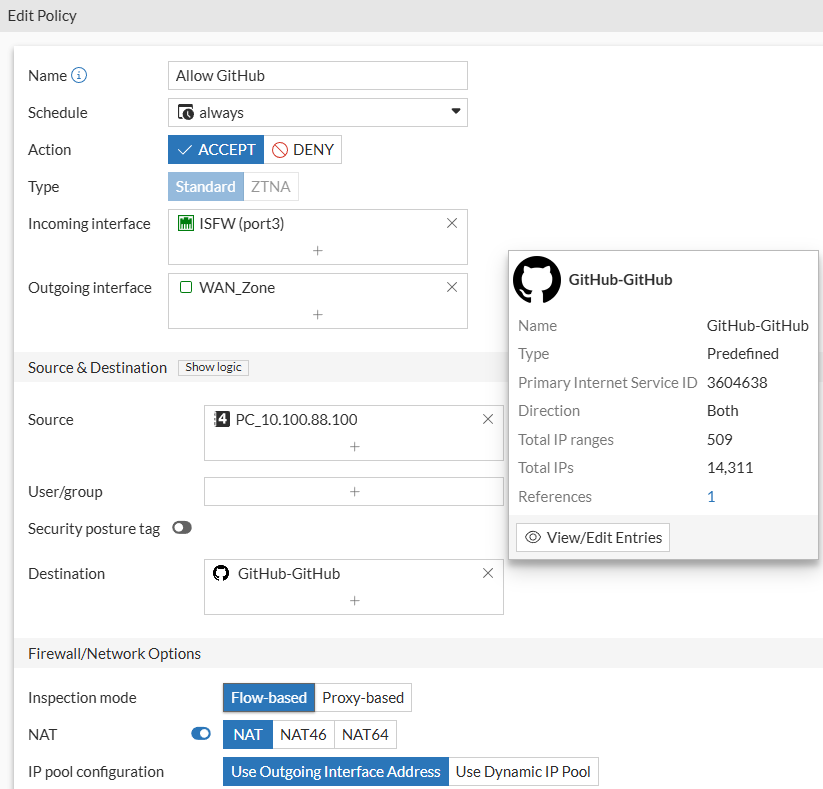
- Configure the remaining policy fields as needed. Then click
OK.
On CLI, the configuration for defining an internet service would be as follows:
config firewall policy
edit 33
set internet-service enable
set internet-service-name "GitHub-GitHub"
next
end
Testing:
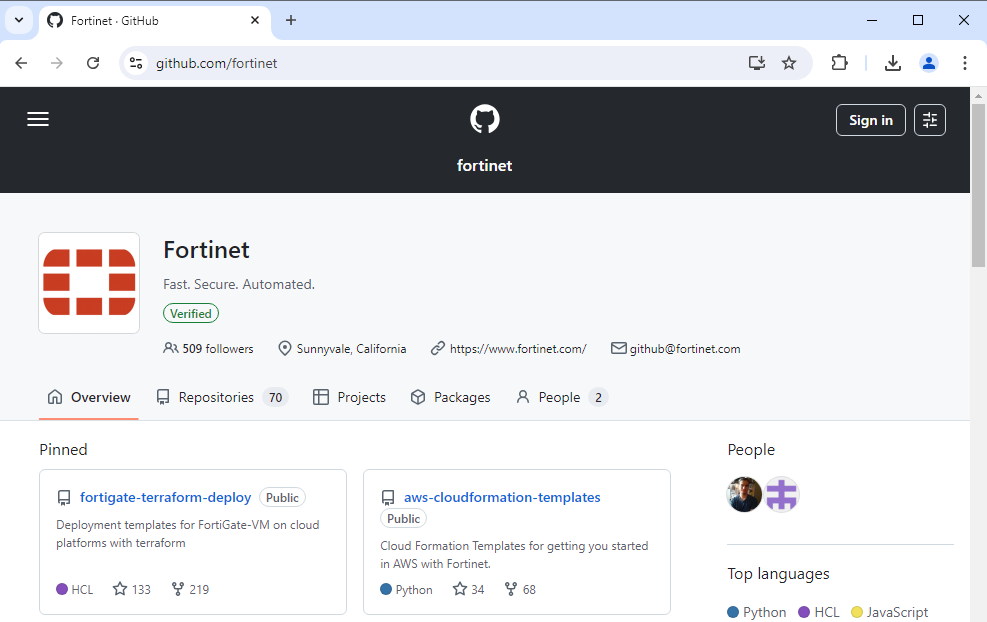
From the client device, test accessing a GitHub profile:
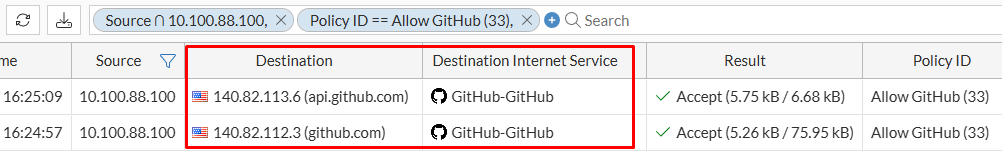
From Log & Report > Forward Traffic verify that traffic is matching the new firewall policy, and the Destination Internet Service is GitHub-GitHub because the destination IPs+ports belong to this service:
Case 2 - More Complex Case#
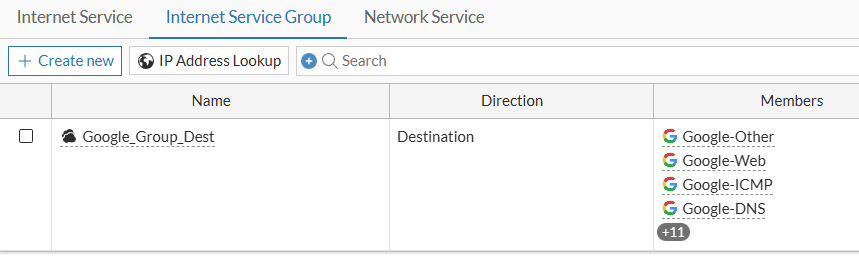
A specific user with static IP 10.100.88.100 needs access to Gmail on the internet. All other traffic destined to internet should be blocked for this user. At the moment, an existing firewall policy is in place blocking user access to the internet. DNS queries are permitted and sent to an internal server.
To enable the user access to Gmail on the internet, a firewall policy with Gmail Internet Service is configured following these steps:
- Go to
Policy & Objects > Firewall Policyand clickCreate New. - Click in the
Destinationfield. - In the
Select Entriespane, selectInternet Servicefrom the dropdown list and search for “Google”:
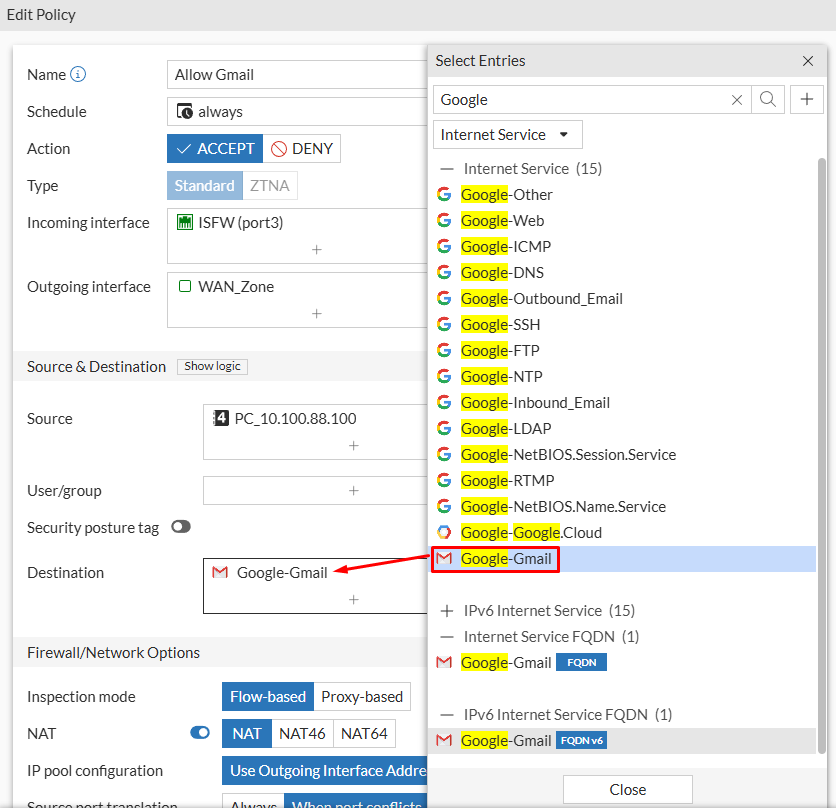
- Configure the remaining policy fields as needed. Then click
OK.
Testing:
From the client device, test accessing gmail.com:
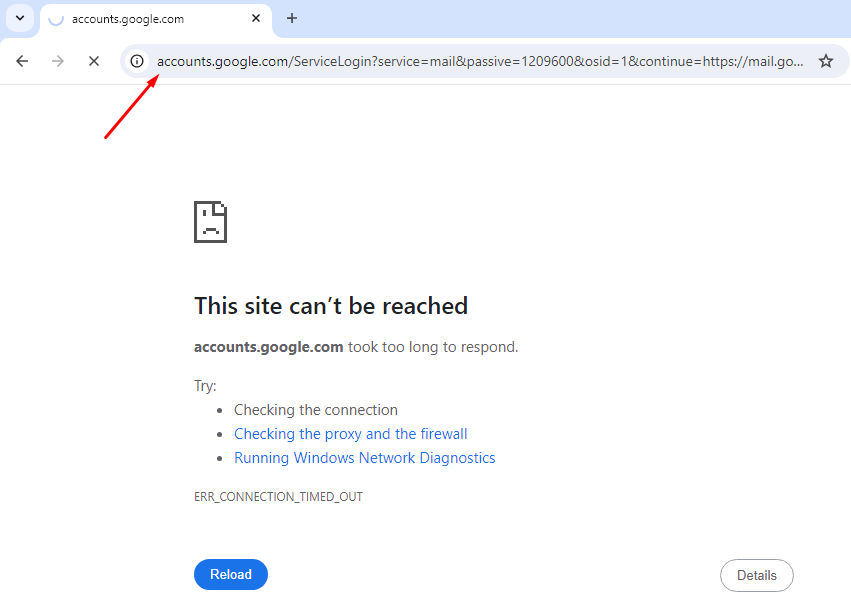
When searching for gmail.com the user is redirected to accounts.google.com because there’s no logged in session.
Under Log & Report > Forward Traffic verify traffic is denied because it’s recognized as Google-Web internet service, which is currently not permitted in the firewall policy:
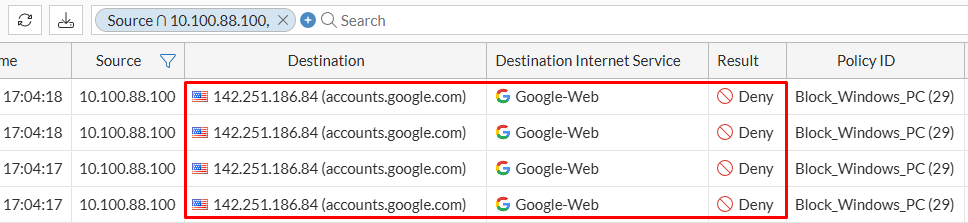
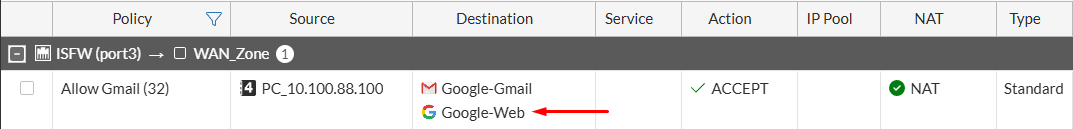
Next, modify the security policy by also adding the Google-Web internet service to be permitted:
This time, the user can login and access the Gmail service:
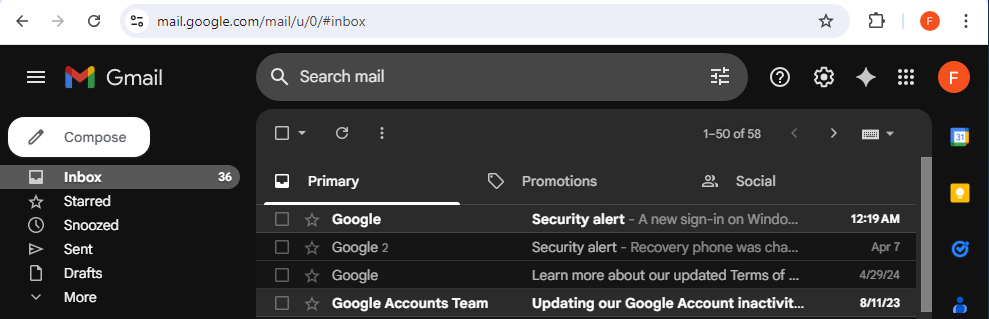
On FortiGate, under Log & Report > Forward Traffic verify that multiple domains/IPs are matched to Google-Web and Google-Gmail internet services:
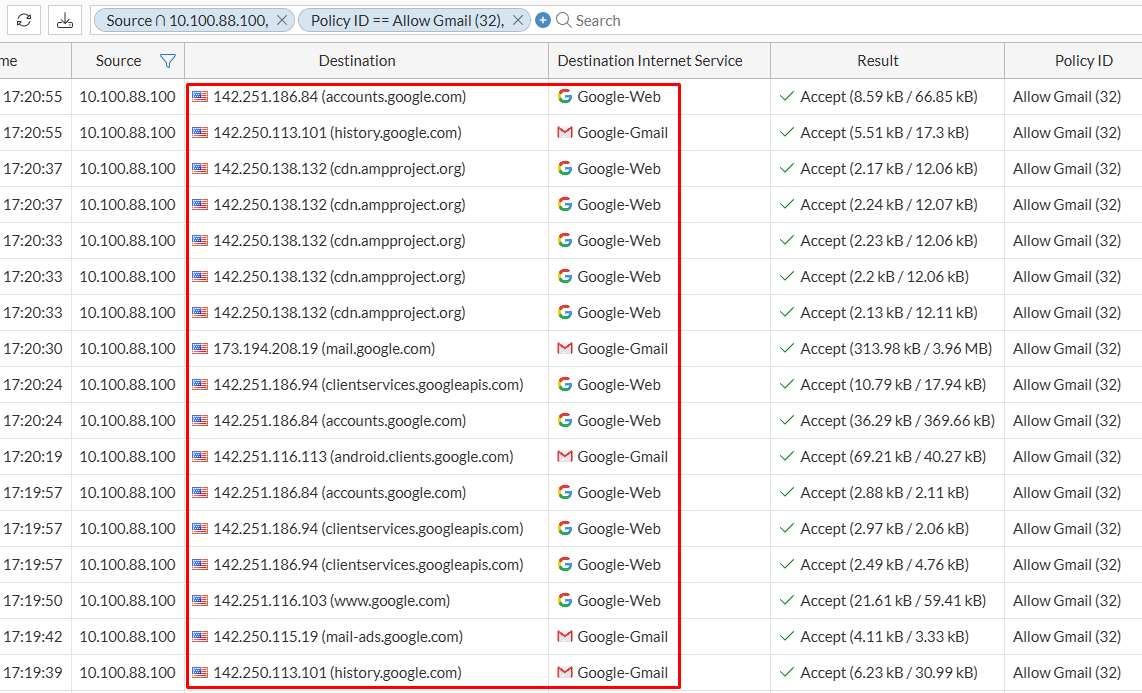
The problem of adding Google-Web as a permitted internet service in the firewall policy is that now, not only Gmail will be allowed. For example, Google searches are not blocked for this user:
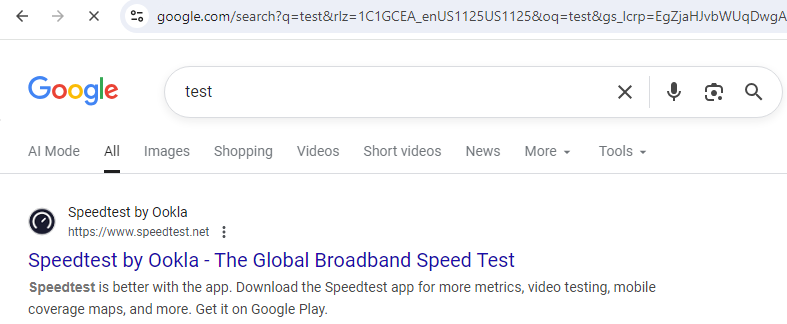
This is not the desired scenario, where only Gmail wanted to be allowed.
Checking Internet Service Details#
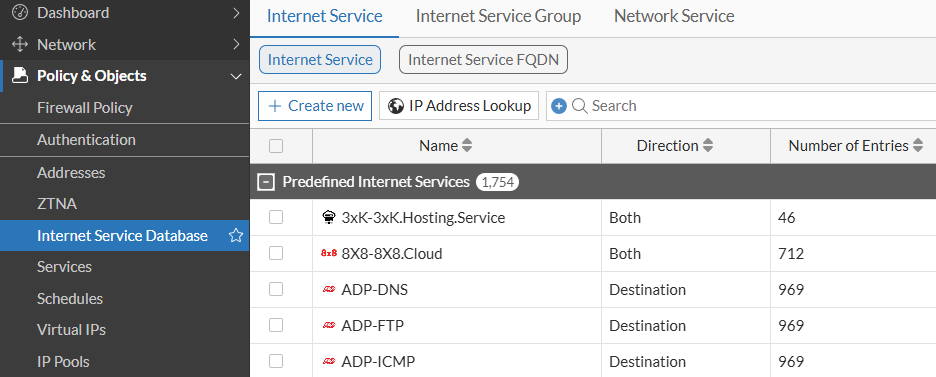
To check what components Internet Services are made of, go to Policy & Objects > Internet Service Database:
- Under
Internet Servicetab, two options are available -Internet ServiceandInternet Service FQDN. The first option has a list ofPredefined Internet Service:
Double click on an Internet Service would give us general information about this service, including its ID, direction, IP ranges, and IPs associated:
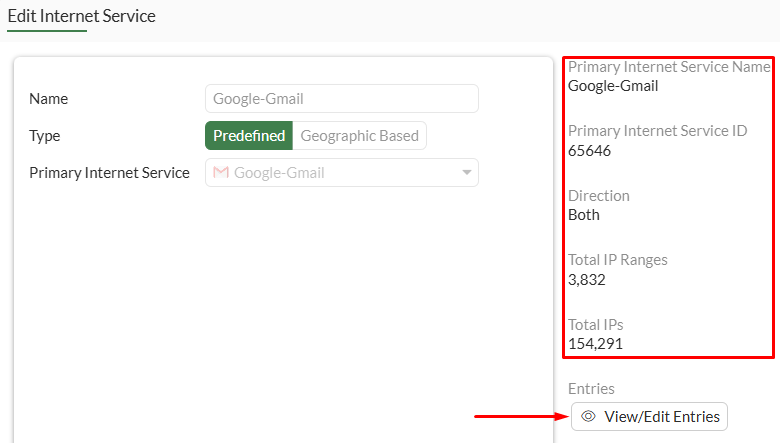
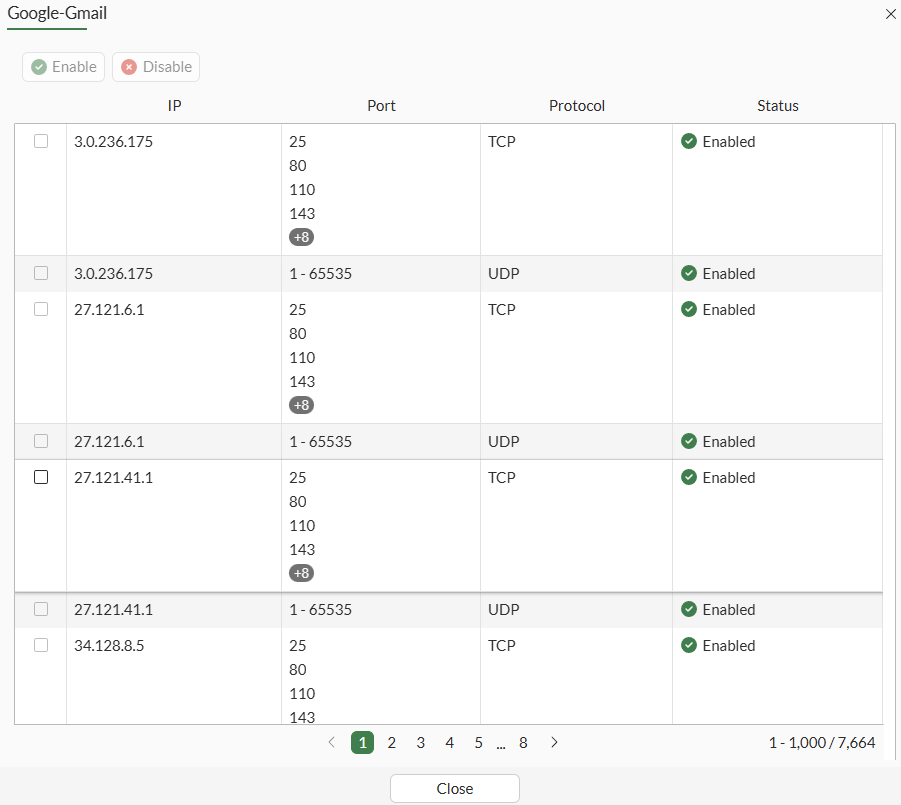
Clicking on View/Edit Entries option of this internet service return all the IPs, ports, and protocols (TCP/UDP) that made up this internet service:
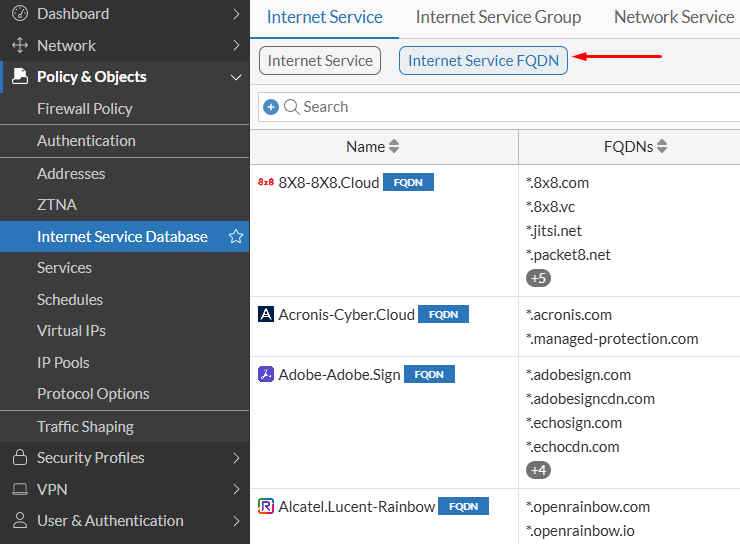
- Selecting
Internet Service FQDN, all the Internet Services composed of domains:
IP address Lookup for Internet Services#
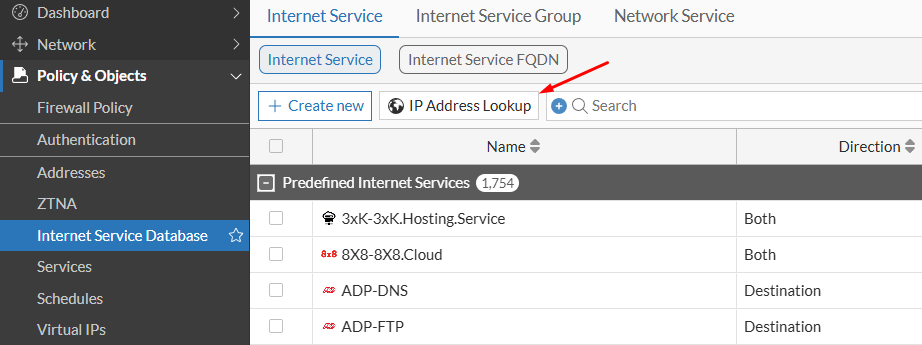
The IP Address Lookup option allows to see to what internet service an IP address belongs to. Under Policy & Objects > Internet Service Database > Internet Service you can find the IP address Lookup button:
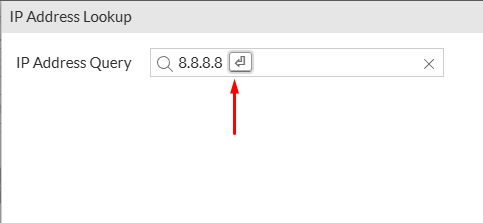
Selecting this option you can type the IP address you want to query:
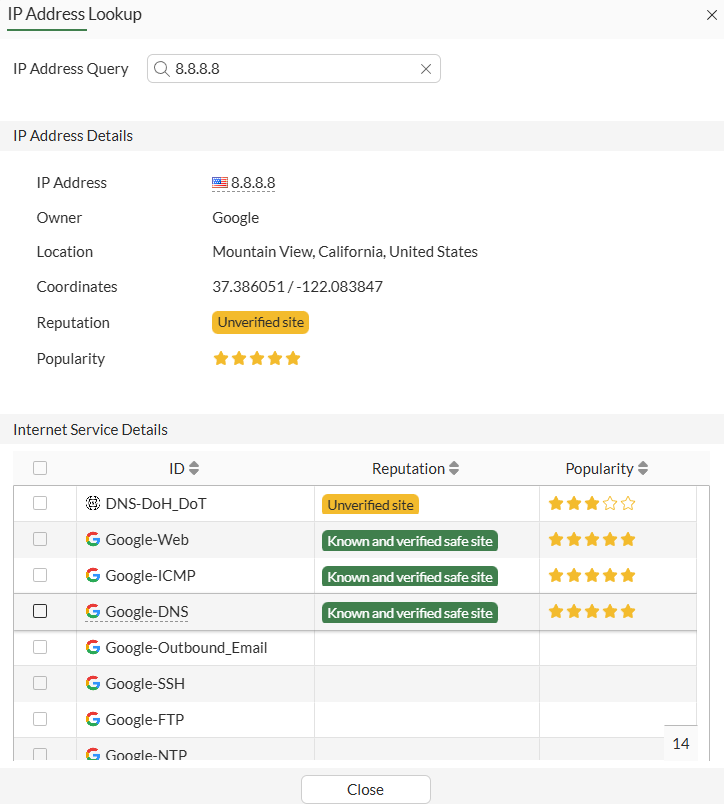
After confirming the query, the IP address and internet service details are shown as follows:
Checking the Version of Internet Service Database#
Beginning in FortiOS v7.0.4 and v7.2.1, a new configuration parameter internet-service-database allows you to select which Internet Service database - full, standard, mini, or on-demand- will be downloaded from FortiGuard.
# config system global
(global) # set internet-service-database ?
mini Small sized Internet Service database with very limited IP addresses.
standard Medium sized Internet Service database with most IP addresses.
full Full sized Internet Service database with all IP addresses.
on-demand Internet Service database with customer selected IP addresses.
Verify the current version of the Internet Service database using the following command:
# diagnose autoupdate versions
...
Internet-service Full Database
---------
Version: 7.04335 signed
Contract Expiry Date: n/a
Last Updated using scheduled update on Fri Sep 19 01:25:21 2025
Last Update Attempt: Sat Sep 20 09:26:05 2025
Result: No Updates
...
In this case, the firewall is using the Full sized ISDB v7.04335
Internet Services Group#
Reference: FortiOS 7.6.4 Administration Guide - Internet service groups in policies
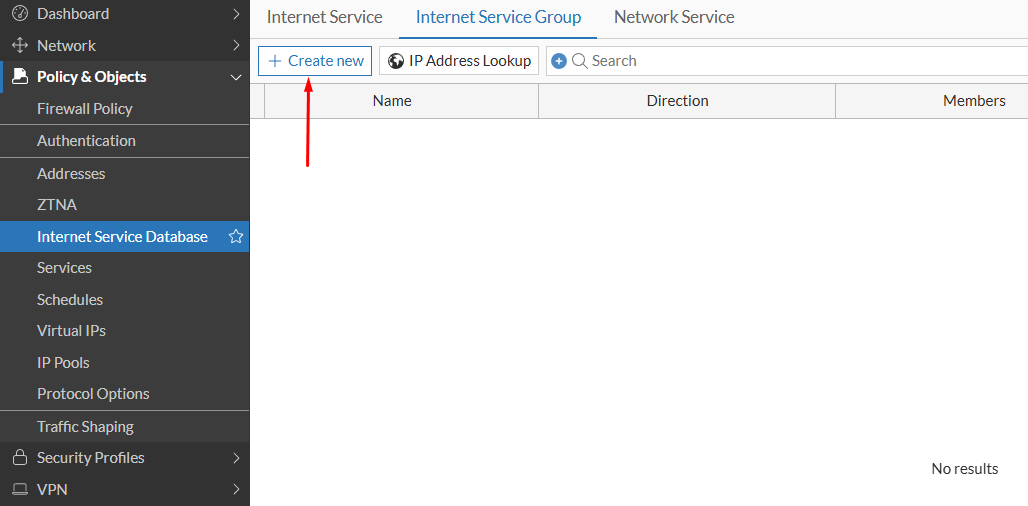
Create an internet service group following these steps:
- Navigate to
Policy & Objects > Internet Service Database, then select theInternet Service Grouptab. ClickCreate New:
- Configure the Internet Service Group specifying in what
Directionit could be possible used and theMembersthat are part of the group:
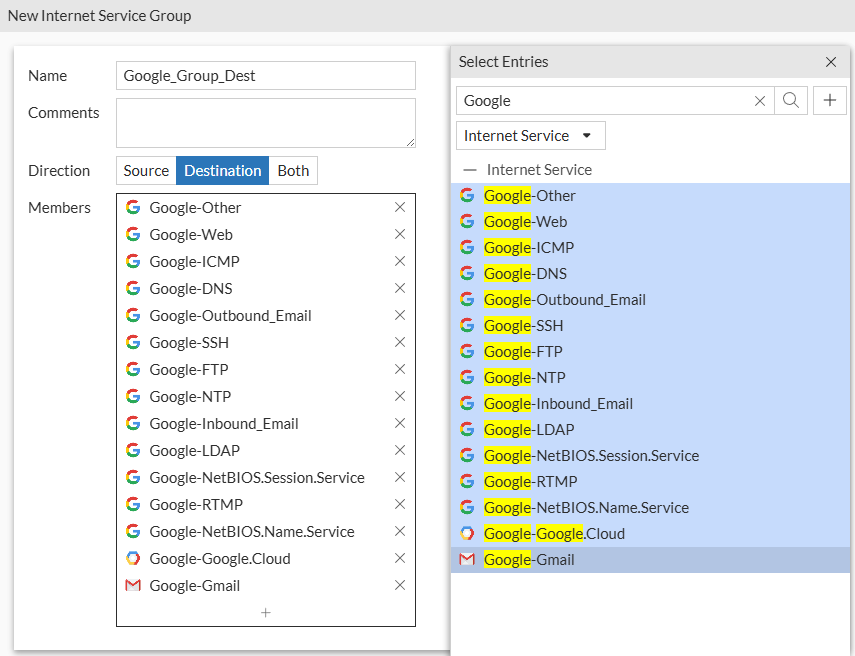
- Click
OK. The internet service is now configured:
Application Control vs Internet Services#
Application Control (AC) and Internet Services (IS) both can be used to identify different services. However each one has a different way of working and different use cases.
Role in Firewall Policy#
On a firewall policy, IS and AC have different roles:
- Internet Services can be used as a matching condition for traffic traversing the firewall. It can actually be used on
SourceandDestinationfields (in replacement of using IPv4 Addresses):
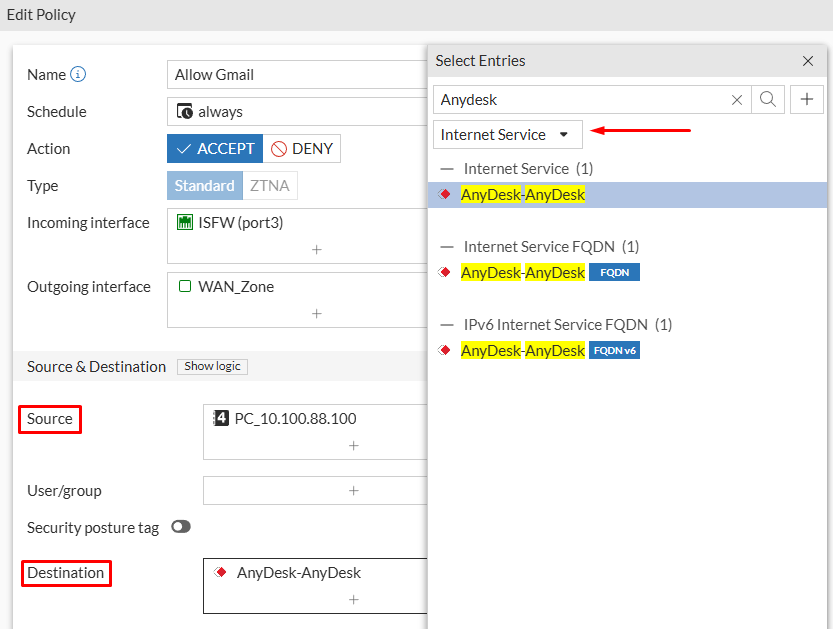
- Application Control profiles are not used as a matching condition compared to Internet Services. Instead, they are used to enforce security on already matched traffic as any other security profile (Antivirus, Web Filter, IPS, etc.):
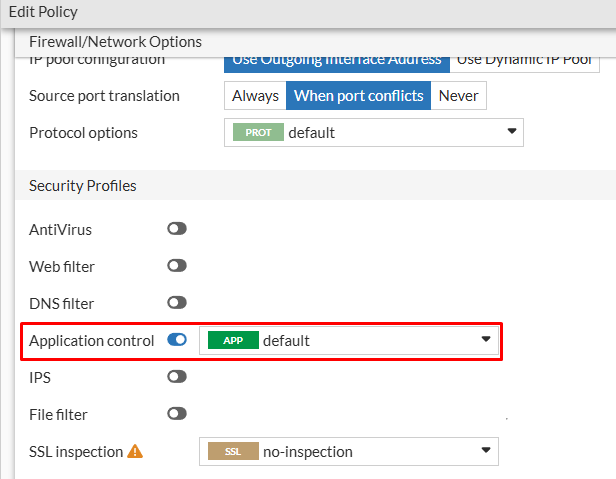
This means that, for traffic matching this policy (based on incoming and outgoing interfaces, source address/user/group/internet service, destination address/internet service, and service) the Application control profile can restrict what applications are allowed or denied.
Granularity#
In practice, you can allow or block a user access to specific internet applications using either Application Control profiles or Internet Services. However, application control profiles provide a better level of granularity.
For example, using internet services, you can allow a user to access WhatsApp service:
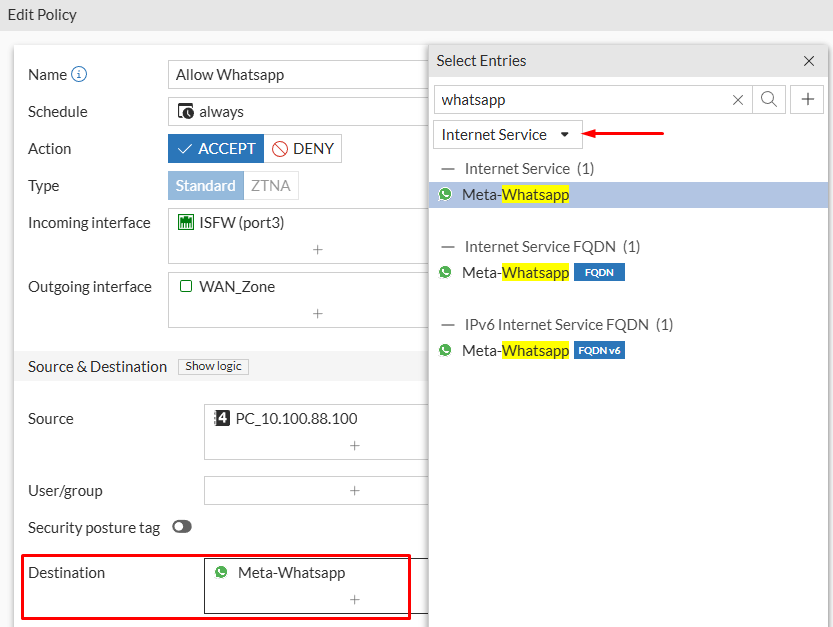
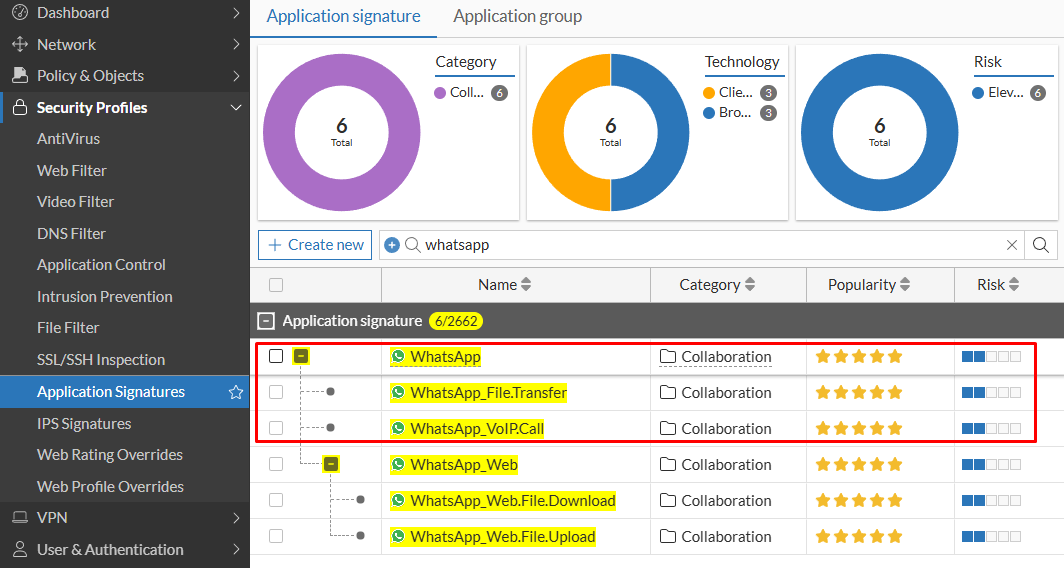
Using application control profiles, you can also allow the “WhatsApp” application. However, you can go even further by allowing/blocking specific services within WhatsApp like file transfer or VoIP calls:
Use Cases#
Although there are some times that you can use Application Control and Internet Service indistinctly, there are also other situations where one of them is more recommended than the other or only one of them can be used to fulfill the requirement.
Application Control use cases:
- You can use AC to allow/block services that are not necessarily related to the internet, e.g. network services like SSH, NTP, FTP, etc. Applications are also identified by the IPS engine even if those services are using non-standard ports.
- Torrents: AC IPs engine can identify and block torrent traffic, which is known for using dynamic ports and peer to peer traffic. This would be almost impossible to block using firewall policies without L7 inspection.
Internet Service use cases:
- You can use internet services for matching traffic to an internet service that should be exempted from deep SSL inspection. This could be because traffic payload is sensitive or the decryption process breaks the website or application (e.g. because it uses certificate pinning). In this case you would only specify the Internet Service as a matching condition on the firewall policy and don’t use a DPI SSL profile.
- If you want to allow/block a specific well-known internet application on a separated firewall policy you should use Internet Services.
Application Control and Internet Services working together:
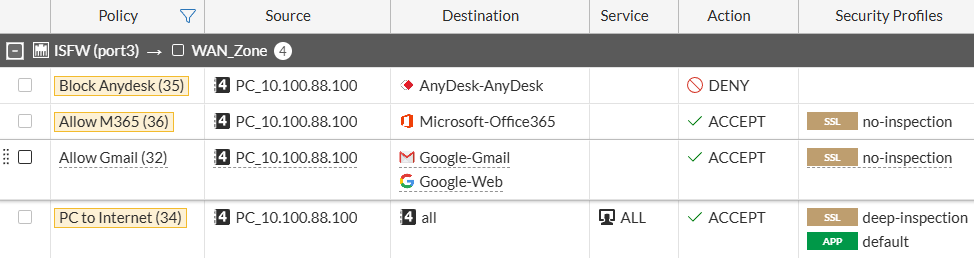
- In practice you can use a combination of AC and IS for managing user access to the internet. You can create higher priority policies for matching specific internet services that you want to allow or block for the source. Additionally, create a policy with lower priority matching any destination together with an application control profile that defines what applications are allowed or denied for the source. This would look something like this:
- There will be other cases where you will want to apply an internet service together with Application Control in the same policy. This is usually required when you want to allow a specific single application defined in the application control profile, however the application is initially recognized as
SSLand then re-identified as the proper application. Filtering down the internet service and theSSLapplication won’t allow the user to access otherSSLapplications.
In the following example only WhatsApp VoIP calls want to be allowed, so Meta-WhatsApp is used as the Destination Internet Service. This by itself would allow all WhatsApp application, so an Application Control profile is also added to nail down the match:
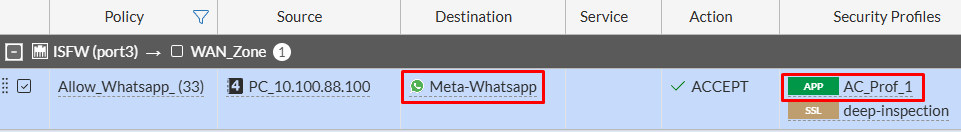
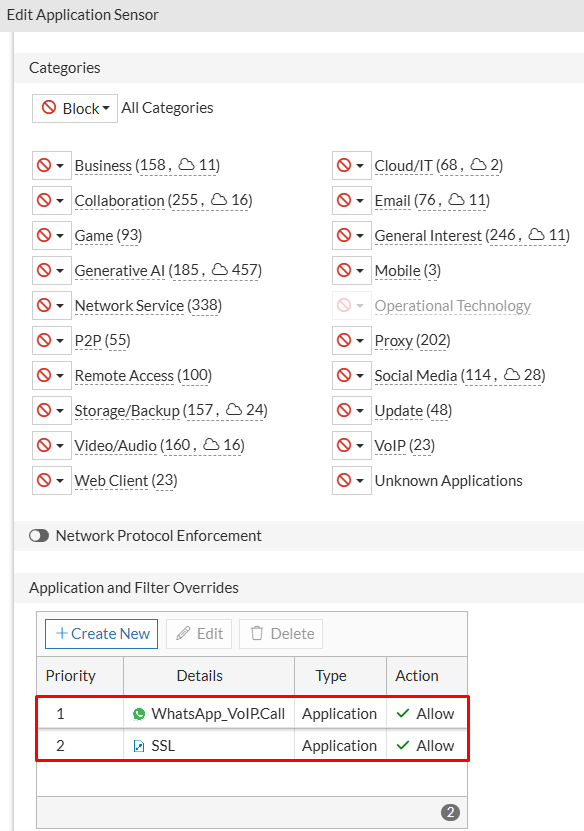
Next, in the application control profile, block all categories and add two application overrides to allow SSL, and WhatsApp_VoIP.Call: